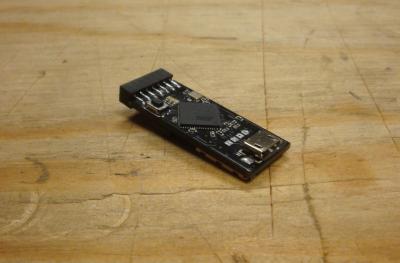
The Glitch
The Glitch is a simple to use, plug-and-play, open source, security testing hardware platform. There are many great "Do It Yourself" security testing hardware projects out there. The problem for most people is the time and expertise it takes to construct and operate them. The Glitch is designed to make open hardware security testing more accessible.
At its core, The Glitch is a reprogrammable microprocessor hardware platform. Through open source development, it can be reprogrammed to work with all sorts of Projects, like Keystroke Injection, Keylogging, etc. Since The Glitch is Ardunio compatible, it builds upon a community of developers to expand its capabilities. It is compatible with a variety of already existing hardware (like Bluetooth, ZigBee, USB, Wi-Fi, ext).
The Glitch is built on open source software. If you want to develop/edit the firmware, you can. Or you can stick with the stock firmware. No need to learn any more about the hardware or software then you have time for. The ability to edit the code makes it possible for anyone to use The Glitch for there own projects. Pinouts allow you to connect additional hardware without the need to solder.
For more about The Glitch and basic usage, see the Documentation.
Hardware
A few major hardware features.
- Reprogrammable Atmel microprocessor
- Small size
- Micro USB connector
- Micro SD reader
- DIP switch
- Solderless pinouts (UART, SPI, I2C, Analog)
- USB solder pads
- Programmable LEDs
Key Features
There are a few key features that make The Glitch ideal for security testing.
- Connection to a computer through USB allows programming and launching payloads. The Glitch does not require any special hardware or drivers to be reprogrammed. It will work on any PC (Windows, Linux, and OSX).
- It it small. The Glitch is only 1.4 by 0.6.inches This makes is convenient to keep in your pocket, backpack, messenger bag, briefcase, suitcase, laptop bag, purse, hat, zombie survival bag, etc.
- Its size also makes it possible to embed in other hardware. As an alternative to the Micro USB plug, USB solder pads make it possible to terminally embed The Glitch into small spaces.
- Users can select from multiple customized payloads to run on-the-fly using the DIP switch on the bottom. A DIP switch is a series of small switches which provide a means for user input. Since there is no keyboard or touch screen, the DIP switch is the only built in method of user input available. Making a selection on the DIP switch instructs The Glitch which actions to perform.
- The Micro SD reader allows for convenient reading, writing, and deleting of files to a regular Micro SD card.
- For projects following the style guide, users can place configuration files, payloads, and help files in Modules on a Micro SD card. A Module is a self contained set of instructions and a payload for The Glitch. The user can specify which modules to execute using the DIP switch. For example, selecting 5 on the DIP switch would launch Module 5 from the Micro SD card. Using self contained modules allow users to bundle up and share their payloads with one another.
- Connectors allow you to connect additional hardware without the need to solder. The Glitch can interact with other hardware through UART, SPI, I2C, digital and analog I/O.
- And most important of all is the community of developers and users. The Glitch can be re-purposed for many different kinds of projects. It would be a shame to just stick with the stock firmware.